In the world of business and great wealth, the value of information is hard to overestimate. With the appropriate data, one can govern the strategy of operation of an enterprise. Confidential information is an item of great interest, and industrial and corporate espionage are becoming more common by the moment.
Companies often hire economical intelligence specialists, who obtain, analyse and provide information, sometimes acquired in a way not exactly legal and ethical. It allows to gain an edge over the rivals, introducing a new technology to the market, or learning about legal and economical condition, and manner of functioning of another economic operator. Nowadays, this threat is also present at the national level ‘ economical intelligence is frequently used for military purposes.
Espionage utilises modern, advanced technology, allowing for listening in, collection of data and quick and effective acquisition and recording of information. Sometimes, planting a bug or a voice recorder is enough, but on other occasions sophisticated technologies are put to use, such as laser microphones or mobile base transceiver stations (so-called IMSI catchers). Is there any way to protect oneself against them? This is where modern technology comes to help.
In business, many crucial conversations are conducted via a mobile phone. Certainly, the data transferred over GSM networks are encrypted (basic authorization and communication encrypting mechanisms are used), but this sort of protection is easy to deal with. The A5 algorithm, which is currently utilised, was broken long time ago – it does not guarantee safety of out conversations any more. Secure calls are possible with telephones offering their own encryption. There are numerous programmatic solutions available, but they are not entirely reliable. A better choice would be to use specialized encrypting phones, such asSecure Phone Enigma E2, product of a British brand Tripleton.
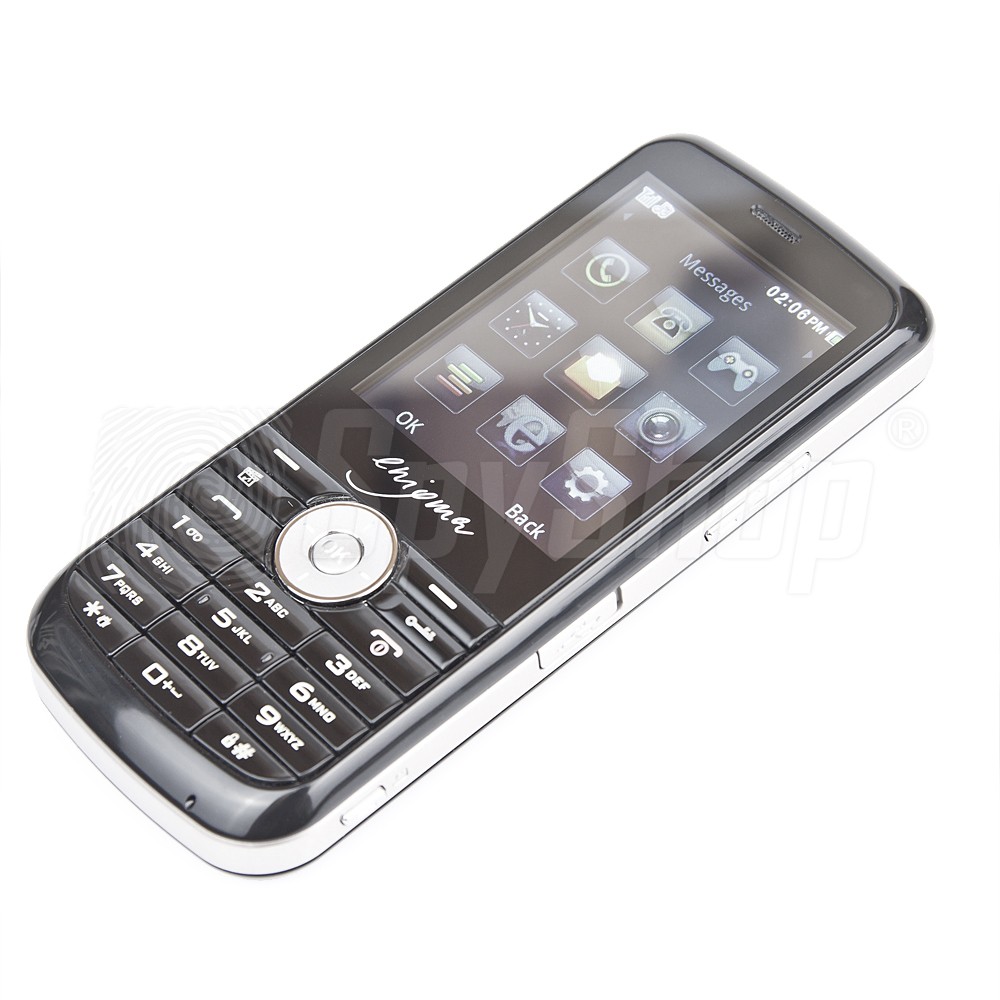
This inconspicuous telephone, looking like a relic of the 1990s, offers surprisingly powerful capabilities. All cryptographic operations are conducted at hardware level, utilising a separate encryption card with encoding coprocessor. It features a self-destruction mechanism triggered in the event of attempted intervention, as well as very strong encryption algorithms. Authentication is conducted with RSA 2048 bit key, signed with SHA-256 hash (which ensures connection to the specified interlocutor, and to him alone), and the transmission itself is encrypted with AES 256-bit algorithm.
The audio circuits are completely separate from the GSM module, and the mobile network is used only to transfer already encrypted information. Due to these precautions, the user can rest assured that nobody will be able to use the information conveyed during a conversation, or in text messages exchanged between two Enigma E2 phones. From the user‘s point of view, using a secure encryption phone does not differ significantly from using a regular phone, thus requiring no specialist knowledge.
Yet another problem faced by security managers and economical espionage protection specialists, is to protect meeting rooms from surveillance. Listening devices, analogue or digital, using various transmission standards (e.g. GSM or WiFi), microphones utilising either wall contact, laser or microwaves, or even a regular voice recorder brought into the room might pose a serious threat to the confidentiality of the conversations. Such a room should be inspected by specialists on a regular basis. To do it, they use electromagnetic spectrum detectors and analysers, vibroacoustic noise generators, causing the walls and structural elements to vibrate, as well as nonlinear junction detectors (NLJD), allowing to detect and localise electronic devices of any type, regardless of being switched on or off, or connected to mains.
Another method of ensuring security of conversations is offered by DigiscanLabs with their Druid DS-600 system. This device was designed to protect from all forms of surveillance. The meeting participants talk through their headsets. The system analyses the sound of their speech, dynamically generating an acoustic signal to mask them. Multiplication, distortion and reverb coming from the speakers renders the sounds in the room incomprehensible, and the signal‘s random and dynamic characteristic is virtually impossible to decipher, making any recordings useless. A single device is capable of conducting a fully secured conversation involving six persons. It is possible to connect two or three modules together, allowing to support up to 18 users.
Protection from listening devices of any kind, and from recording the conversation, is a major asset of the device. Its mobility and quick assembly allow to use it in any room without prior preparation. Due to a battery power supply, Druid DS-600 is capable of operating in any condition, which might prove especially important while conducting vital negotiations in unfamiliar areas.
There are reliable solutions available, that can minimize the risk of leakage of confidential data. However, it should be remembered that the human being – and human mistakes – are the weakest link. Therefore, apart from utilising technological precautions, it would be advisable to undergo a training in information security, and to devise appropriate procedures.
Detective Store is a distributor of Tripleton and DigiscanLabs products.










Leave a Reply