Add a review
-
Compliance with the description:
-
Durability:
-
Quality:
-
Usability:
Hello, if you already have an account, log in.
Attention! We have switched to a new store engine!
Our online store switched to a new IT infrastucture on February 23, 2023. Old accounts created before 23.02.2023 still work and you can easily log in using your old access data. However, your purchase history from before 23.02.2023 is no longer visible in your accounts. If, as an old customer, you need your data for previous orders (placed before 23.02.2023), please contact us by email.
You are a new user?
Create an accountCart: (0)
You do not know where to start?
See recommended products
Remote keylogger for discreet PC surveillance - SpyLogger Classic ®
118,78 $ VAT included
Product unavailable!
Order a similar product: SpyLogger Pro Cloud - remote employee computer monitoring .
In the contemporary world computers are simply irreplaceable. Computer has become a tool of work, learning, entertainment and socialisation. However, computer security is not something we can treat lightly. The Internet is full of lurking dangers. Both children making new friends and unaware adult users utilizing paid services can easily fall prey to data theft. If you are an employer, you may also consider protecting your computer from dishonest employees who use it for private purposes. This spy software allows you excatly that.
SpyLogger Classic® is a remote keylogger software designed to support discreet and efficient computer surveillance. It allows us to supervise our child browsing the Internet, control our employees, and protect our data from unauthorized access.
To start with, this remote keylogger for dscreet PC surveillance gives you access to information about every keystroke and generates screenshots in specific pre-set time intervals. The user is given a full picture of all computer activities, including every website address typed in the browser’s address bar, access to all internet communicator and chat conversations, and passwords to social media profiles. SpyLogger will record all Facebook, Skype and other similar application activities and take a screenshot, which can help you to identify the receiver of the video call. The latest version of keylogger software allows you to track both file modifications and USB drives.
The remote keylogger software can be configured on any computer and the installation process takes less than 30 seconds to complete. Included manual gives you clear and easy-to-follow instructions about the whole process.
Finally, you are given unlimited 12-month warranty!
All collected text logs and screenshots can be copied from monitored computer by connecting SpyLogger ® device. They can be subsequently viewed on any device. 8 GB memory is enough to collect data for a timespan of about 200 to 240 days.
The spy software is able to capture and record all keys which have been pressed. It also allows for better support of international and special characters. The data are saved as HTML file that can be opened in any standard browser.
SpyLogger Classic ® generates screenshots at a fixed time and saves them in JPEG format. Remote keylogger allows the user to access not only the records of pressed keys, but also browsed pictures, contents of received e-mails and conversations through instant messaging or chats.
Every time a certain key word is typed SpyLogger ® spy software generates an additional screenshot.
SpyLogger ® stores data about all running applications as well as all window opening, closing and switching procedures.
Logging all actions performed on files (open, move and many other), including time and date of the modification. Remote keylogger also makes it possible to filter files by type or to select only specific folders.
SpyLogger ® checks which of removable storage devices (CD/DVD or USB) were used on the computer and informs about every unauthorized access to our data.
The remote keylogger gives the opportunity to prepare configuration at any computer, which is crucial when access to the monitored computer is very limited. The subsequent installation on the target device will take only about 30 seconds.
Due to the constant upgrading process, SpyLogger ® is invisible to antivirus programs.
SpyLogger ® is completely invisible to computer users. It uses only a fraction of system memory, has no icon or name, and leaves no traces behind.
The spy software can be run in Windows XP, 2000, 2003, Vista, 7 and 8. An installation does not require administrator account but the monitoring works only on the account on which SpyLogger ® was installed. In case you need to monitor different accounts, you should install SpyLogger ® software for each account separately.
SpyLogger ® program is stored on a USB drive (8GB), which allows you to install, download, copy and delete data. You should remember that the device works automatically and should be removed from the USB port at the end of each process.
12 months warranty on remote keylogger with access to on-line update and repair service. USB drive is covered by a lifetime warranty.
On some computers running Windows XP, a sound card does not support the "What You Hear" function. In this case only one side of a conversation might be recorded. It does not apply to computers with "What You Hear" driver as well as Windows Vista, 7 and 8 systems.
After connecting the USB drive to the computer the only thing to do is to run SpyLogger manager. It allows you to
ON-LINE UPDATE AND REPAIR
Link to manual update and repair on-line
SpyLogger ® setup  SpyLogger ® configuration
SpyLogger ® configuration 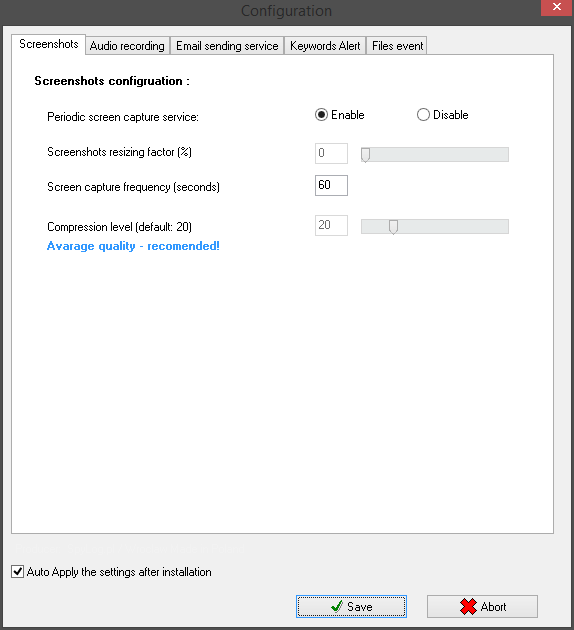
The amount of collected data is limited only by the SpyLogger ® memory. 8GB of memory is usually enough to collect data for about 200-240 days. It is advisable to copy SpyLogger data on a regular basis. If the mail service is enabled, the number of messages you can receive is limited by your e-mail account capacity. It is advisable to use google account because of its speed, stability, and the amount of free disc space.
Model keylog 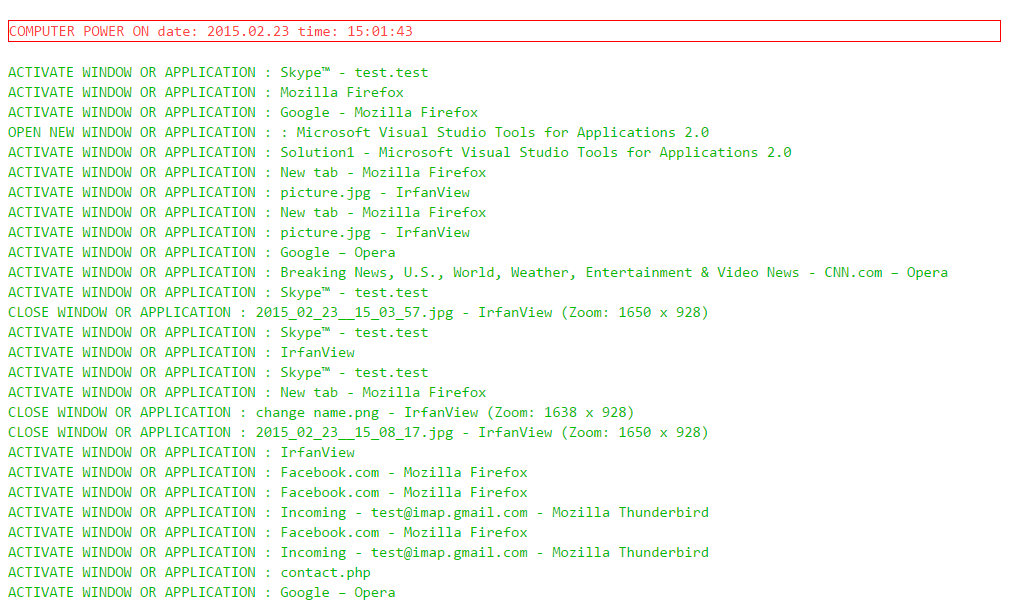 Model screenshot
Model screenshot 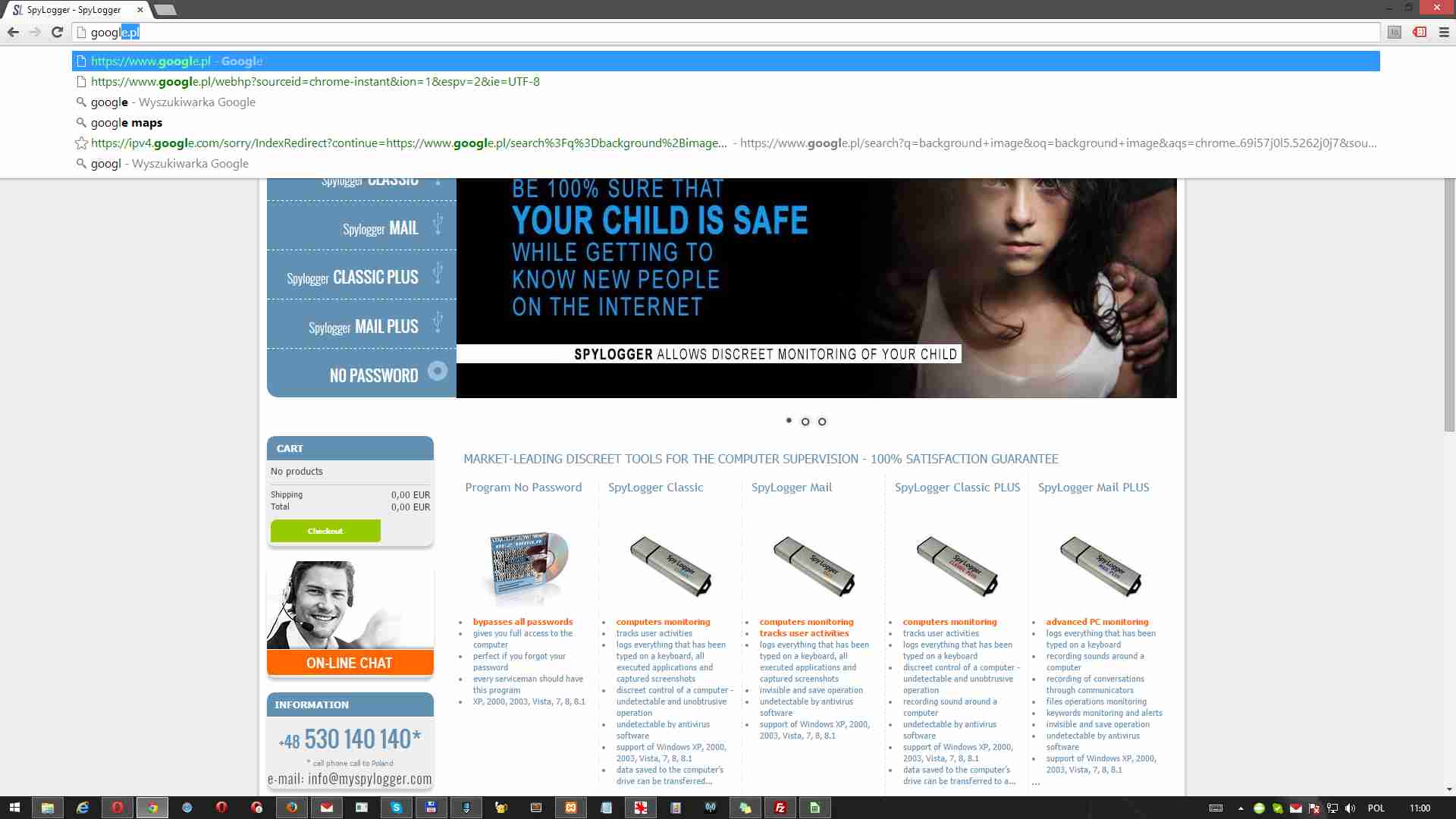
Attention!
Remote keylogger SpyLogger ® software is also available in Polish and German language version.
| SPYLOGGER CLASSIC | SPYLOGGER MAIL | SPYLOGGER CLASSIC PLUS | SPYLOGGER MAIL PLUS | |
|---|---|---|---|---|
| Keyboard monitoring | ||||
| Saving screenshots | ||||
| Saving visited websites | ||||
| Call recording via instant messaging | ||||
| Recording of sounds in the environment | ||||
| Analysis of running programs | ||||
| Direct downloading of data | ||||
| Sends data directly to mailbox | ||||
| Warranty of the advanced keylogger software for parental control | 24 months | 24 months | 24 months | 24 months |
| Warranty on the pendrive | lifetime warranty | lifetime warranty | lifetime warranty | lifetime warranty |
Overall rating
Availability: On order
202,35 $ (brutto)
Availability: Available
134,45 $ (brutto)
Availability: Available
148,03 $ (brutto)
Availability: Available
191,21 $ (brutto)
Please sign in first.
Sign in