How to protect an important conference? Is it possible to encrypt phone conversations? Businessmen and entrepreneurs need modern data protection solutions. These may be available through easily accessible and highly efficient technologies.
During last weeks we realized that almost everybody may obtain an access to confidential conversations. This fact encouraged businessmen to implement and use anti-spy devices. The stake is the strategic company‘s data. Data which are hunted for by the rival companies. The market offers a wide scope of anti-wiretapping systems. Which are the best to choose and how to use them?
Confidentiality with a phone
In a world of business many important conversations are conducted via telephone. The surveillance specialists are fully aware of this fact. Although the GSM data is encrypted but cracking the algorithm is not a tough task for a specialist. That is why the mobile networks wiretappings are considered one of the simplest methods of obtaining confidential information.
Is a ‘safe‘ conversation via telephone possible at all? Of course. However, it requires different encryption methods than used in telephones based on software solutions.
The subject is so called hardware encryption – the most effective data protection solution for GSM network conversations. It is used e.g. in Enigma E2 telephone, operation of which is based on two-step encryption process – authentication and encryption of the conversation. Apart from that, its construction contains anti-wiretapping modules, completely isolated from the rest of the system.
How the Enigma really works?
The first step of connection includes confirming the identity of callers. It is not aimed at specific persons but rather at the devices they are using. The encrypted connection requires two telephones. During the process of authentication, the 2048-bit certificate is generated, encrypted byt he RSA key and signed by SHA256 contraction. It is important to say that according to most of experts, breaking the RSA key could be a task for even few years for the person who is wiretapping the conversation. This shows how efficient methods are implemented in the Enigma E2 device.
What happens after the conversation is authenticated? The sound is encrypted with 256-bit AES algorithm. Such protected data are passed to the GPS module and, as encrypted data, enter the mobile network.
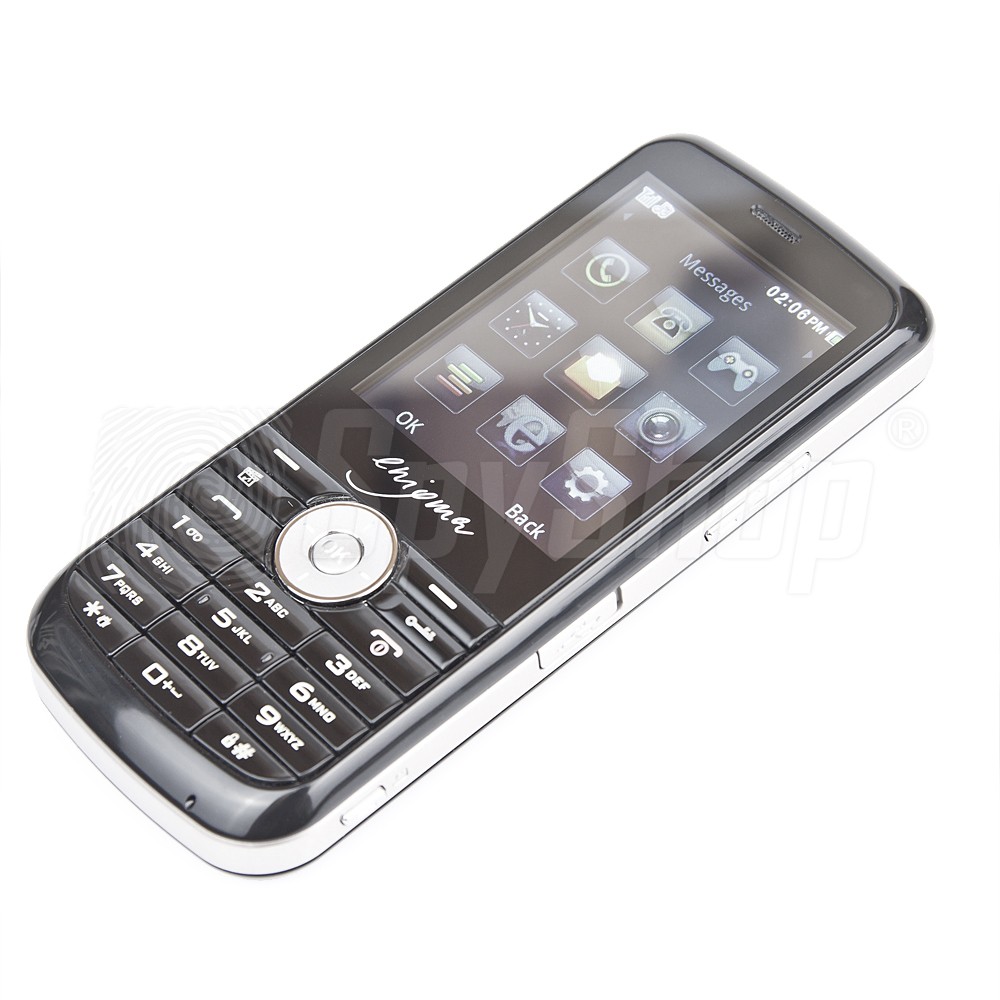
A dedicated encrypting card of the Enigma which contains the controller with cryptographic co-processors and hardware random number generator and isolation of audio system from the GSM system cause that trasnferring the non-encrypted sound via radio is almost impossible. These elements and realatively simple construction of the device – no WiFi technology and applications permanently connected to the Internet cause that the phone based on two-step hardware encryption is absolutely one of the most effective solutions in business conversations protection.
Searching for the bug
You may ask now ‘ what about the bugs and spy voice recorders? The remedy may be found for these too. The best way is to buy a cheap radio frequency scanner which detects all the analog and digital transmissions. The more efficient solution is so called nonlinear connections detector. It detects every electronic device independently of the type, even of the fact the device is turned off. You may detect the classic voice recorder using this equipment which could not be possible with radio scanner. These solutions may be used outside the offices, in secluded restaurant rooms, clients‘ or partners‘ buildings.
Interesting example is the Raksa detector which, apart from its good value for money, offers a wide scope of functions. Needless to say, it may protect you from GSM network wiretapping or from GPS localizer.
This solution is still a protection against simple methods of wiretapping. In places where confidential information may involve serious incomes, more sophisticated equipment is needed.

Safe conference room
High-end wiretapping equipment is so advanced that they provide the possibilty of surveillance without enetering the room where the targets are. Laser microphones do not even require to be near the talking people. All you need is a convenient view of the window of the room. Such wiretappings are better to jam than to detect.
Acoustic systems are perfectly fit to this task. They protect the whole rooms, making them some kind of cages. Cages, which protect the sounds of conversations from being intercepted.All what a potential spy could hear was only a random noise.
Druid DS-600 is such a system. It is one of the most popular devices destined to protect the conference rooms and important meetings and summits. In this case, the talking people communicate with special headphones sets. The nearby transmitter generates acoustic interference ‘ impossible to remove from the recording.

The below material may be treated as a review of wide spectrum of devices for wiretapping protection. All of these can be found on our website. It happens that the cheapest ones cost up to 40 GBP. That is why I encourage you to become familiar with our offer containing detectors and jamming devices. Confidentiality of information is a basic for every well prospering business. Are you anxious concerning the fact that nowadays‘ hackers and hired specialists may intercept even the top secret data with such an ease?










Leave a Reply