-
<div class="category_banner" style="background-image: url('/img/cms/en/professional-equipment-55.jpg');">
<div class="wrapper">
<div class="categoryName">
<h2><span class="icon-stop"></span>Professional spy equipment</h2>
</div>
<div class="clearfix"></div>
<div class="categorySentence">
<p>Highest quality equipment</p>
</div>
</div>
</div>
<h2>Spy equipment for experts</h2>
<p><strong>Detective Store</strong> is a dynamically evolving brand that puts an emphasis on providing equipment of the highest quality, and the most advanced technology. Our presence at detective industry conventions allows us to improve our range of products, not only for individual clients but primarily <fo></fo> professional users such as: members of the uniformed services, specialists in the field of information security, as well as private security companies.</p>
<p><strong>Detective Store</strong> offers devices of the highest quality for a wide range of requirements.</p>
<p>Specialist equipment available at Detective Store includes solutions which will be of interest to those who are just beginning their adventure with detective work or have suspicions that someone is monitoring them. In such a situation, hidden listening device, spy camera and GPS locator detectors may prove helpful. The products presented in the shop will meet even the most demanding requirements and their operation is very simple and discreet. The sensitivity of the detectors allows the detection of transmission even from a distance of several metres, so that the entire operation does not arouse suspicion. When choosing a model for yourself, it is worth taking into account the number of operating modes. Thus, depending on the situation, you can use the silent, vibrating, visual or audible mode. Fast and precise operation is also an advantage of acoustic counter-surveillance systems, which fully protect conversations from eavesdropping.</p>
<p>Hand-held metal detectors are products that should interest you when organising a mass event. Resistance to damage, durability and high sensitivity are features that should be included in the product you decide on. In the offer of SpyShop.pl you can find models valued and used by the uniformed services. For the most demanding customers, for whom security is extremely important, the brand has prepared handheld explosive and drug trace detectors. When thinking about a wide, professional activity, it is worth considering the purchase of professional voice recorders with Wi-Fi connectivity, X-ray scanners and laser microphones that also work through glass and walls.</p>
-
<div class="category_banner" style="background-image: url('/img/cms/en/explosive-materials-detectors-175.jpg');">
<div class="wrapper">
<div class="categoryName">
<h2><span class="icon-stop"></span>Detection of chemicals</h2>
</div>
<div class="clearfix"></div>
<div class="categorySentence">
<p>Security and precision</p>
</div>
</div>
</div>
<p>Detecting and identifying chemicals is a key task for security services such as border guards. Airports, for example, use specialized equipment to detect explosives and illegal chemicals, ensuring the safety of travelers. These tools are also indispensable during mass gatherings. Laser explosives detectors can detect chemical substances in seconds, and chemical identification applies not only to banned substances, but also to those that may pose a threat.</p>
<p><strong>Chemical detectors are able to quickly and accurately detect the contents of a substance, regardless of its condition.</strong></p>
<p>In such workplaces where explosive or flammable substances are present, such as production halls, warning gas detectors are used, which signal the presence of dangerous gases by sound. One- or two-gas meters are available, suitable for specific types of gases. Safety is a top priority.</p>
-
<div class="category_banner" style="background-image: url('/img/cms/en/criminology-165.jpg');">
<div class="wrapper">
<div class="categoryName">
<h2><span class="icon-stop"></span>Forensics</h2>
</div>
<div class="clearfix"></div>
<div class="categorySentence">
<p>Data extractor</p>
</div>
</div>
</div>
<h2>Extraction, decoding and analysis</h2>
<p><b>Forensics</b> is the science of collecting, analyzing, and presenting digital evidence from various sources, such as mobile devices, computers, cloud services, and more. Forensics can <b>help investigators solve crimes, uncover fraud, protect data, and recover lost information.</b></p>
<p>The need to combat crime and terrorism in the world is growing every year. The most vulnerable places to attack are public places, airports, courts or penitentiaries. In such places it is necessary to provide innovative laser explosives and drug detectors, both in liquids and powders. It is worth betting on high quality products offered by Detective Store, because it is on such equipment that it depends whether smuggling or an attack is thwarted. <b>Software for rapid filtering of data</b> or its extraction, decoding and analysis may also prove indispensable. When deciding on a purchase, it is worth investing in equipment dedicated to and used by investigative or intelligence agencies.</p>
<p>One of the most advanced and widely used tools for forensics is the <b>Cellebrite UFED</b> (Universal Forensic Extraction Device), which enables law enforcement, military, intelligence, and corporate security professionals to access and collect data from a wide range of digital devices, including smartphones, tablets, drones, SIM cards, SD cards, GPS devices, and more. <b>UFED can extract data from locked, encrypted, damaged, or deleted devices, using multiple methods such as logical, file system, or physical extraction.</b> UFED can also analyze and visualize the extracted data, using powerful software such as Cellebrite Physical Analyzer, Cellebrite Pathfinder, and Cellebrite Inseyets.</p>
<p>As an <b>authorized distributor of Cellebrite</b>, we offer the best solutions for your forensics needs. Whether you need UFED hardware, software, training, or support, we can provide you with the most reliable and cost-effective options. We have years of experience and expertise in the field of forensics, and we are committed to helping you achieve your goals and overcome your challenges. We also provide special training courses and certifications for Cellebrite products, which will help you master the skills and techniques required for successful forensics investigations.</p>
-
<div class="category_banner" style="background-image: url('/img/c/systemy-taktyczne-i-ratunkowe-171.jpg');">
<div class="wrapper">
<div class="categoryName">
<h2><span class="icon-stop"></span>TACTICAL AND RESCUE SYSTEMS</h2>
</div>
<div class="clearfix"></div>
<div class="categorySentence">
<p>Professional wiretap</p>
</div>
</div>
</div>
<h2>Tactical and rescue systems</h2>
<p>Detective Store offers professional devices for surveillance. One of them is called RETWIS. It is a professional radar specialized in location of people behind the wall.</p>
<p>An interesting item is a tactical rescue system that enables 3D vision through walls. These types of products, depending on the selected variant, are reliable even from a distance of 40 metres, also working through wood, bricks and concrete. As a result, they have found applications not only in the police, but also in the army or in rescue services. Military night vision binoculars are also equipment used in special operations, as is the GSM and UTMS activity positioning system. In our offer you can also find mobile systems for detecting people in vehicles, which is certainly applicable not only for refugees, but also for prison fugitives. The mobile phone detection system will also find its application in prisons.</p>
-
<div class="category_banner" style="background-image: url('/img/cms/en/174-nljd.png');">
<div class="wrapper">
<div class="categoryName">
<h2><span class="icon-stop"></span>Detection of electronic devices</h2>
</div>
<div class="clearfix"></div>
<div class="categorySentence">
<p>Counter surveillance</p>
</div>
</div>
</div>
<h3>Specialized spy detectors</h3>
<p>Detectors of electronic devices are advanced tools for <strong>counter surveillance</strong>. By using detectors offered by Detective Store you can prevent from being eavesdropped. They can be used for inspection of companies, banks, conference halls, house rooms, or correctional facilities. They help with searching of surveillance equipment such as: listening devices, mobile phones, chip cards and cameras. The range of particular detectors varies, according to the needs of our customers. Choose one appropriate for you.</p>
-
<div class="category_banner" style="background-image: url('/img/cms/en/categories/Baner-imsi-catchers.jpg');">
<div class="wrapper">
<div class="categoryName">
<h2><span class="icon-stop"></span>IMSI Catchers</h2>
</div>
<div class="clearfix"></div>
<div class="categorySentence">
<p>Unmatched efficiency</p>
</div>
</div>
</div>
<h2>IMSI Catchers</h2>
<p>Discover the pinnacle of covert monitoring technology with IMSI Catcher systems. Engineered to operate seamlessly within 2G, 3G, and 4G mobile networks, this advanced solution offers undetectable surveillance capabilities for tracking and intercepting SMS text messages and voice calls, both incoming and outgoing.</p>
<p>Once a target is identified, operators gain access to real-time monitoring and interception of two-way GSM transmissions, including outbound communications from the target and incoming transmissions to the target and a designated receiver. Additionally, our system offers remote manipulation capabilities, allowing for the blocking, redirection, or modification of intercepted communications.</p>
<p>Enhancing surveillance operations further, IMSI Catchers offers advanced features for target localization through triangulation within the existing mobile network infrastructure. While the accuracy of positioning may vary based on base station density, our system also provides remote activation of GPS locators embedded within the target's device.</p>
<p>Experience unparalleled surveillance capabilities with IMSI Catcher systems, providing unmatched efficiency and discretion for your monitoring needs.</p>
-
<div class="category_banner" style="background-image: url('/img/cms/en/categories/Baner-encrypted-phones.jpg');">
<div class="wrapper">
<div class="categoryName">
<h2><span class="icon-stop"></span>Encrypted Phones</h2>
</div>
<div class="clearfix"></div>
<div class="categorySentence">
<p>Complete protection</p>
</div>
</div>
</div>
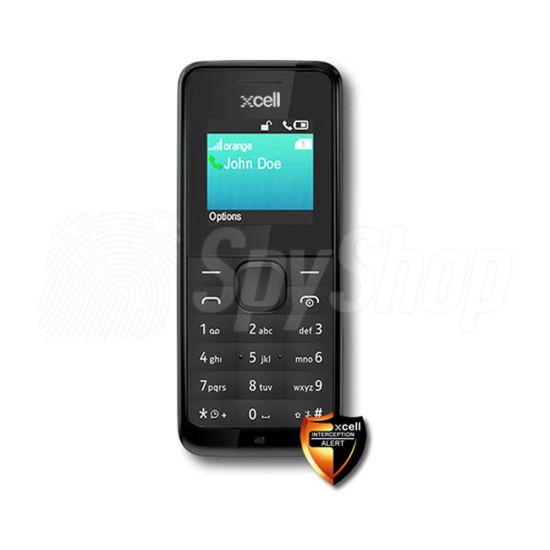
<h2>Encrypted phones</h2>
<p>Encrypted phones are devices equipped with sophisticated encryption technology that ensures the privacy and security of calls and messages exchanged between users. This technology, known as end-to-end encryption, has gained significant attention in recent discussions about safeguarding digital communications.</p>
<p>End-to-end encryption functions by encrypting data on the sender's device before it is transmitted and decrypting it only upon arrival at the recipient's device. This process ensures that communications remain confidential and inaccessible to any third-party interceptors, as the transmitted data appears as unintelligible gibberish to unauthorized entities.</p>
<p>In encrypted phone calls, end-to-end encryption secures both voice and text communications, providing users with a secure means of conducting conversations. Popular messaging and calling applications such as Signal, WhatsApp, Telegram, and Google Duo incorporate end-to-end encryption to protect user data from unauthorized access.</p>
<p>For Android devices, Google Duo offers built-in encryption for secure calls, while apps like Signal provide additional encryption options. Similarly, iPhone users can utilize encryption features available in apps like Signal and WhatsApp to ensure the confidentiality of their phone calls.</p>
<p>The process of end-to-end encryption involves the generation and exchange of encryption keys between sender and receiver devices. These keys serve as the means to decrypt the encrypted data, allowing users to access the original content of their communications securely.</p>
<p>In summary, encrypted phones equipped with end-to-end encryption technology offer users a reliable solution for safeguarding their conversations and messages from potential eavesdropping or interception, ensuring privacy and security in an increasingly interconnected digital world.</p>


 Signal
Signal